Designing a Global Measurement Infrastructure to Improve Internet Security (GMI3S)
We propose to design and prototype a distributed, integrated infrastructure to measure the Internet, with the objective of improving Internet infrastructure security.
Work done in collaboration with subcontractors at MIT's Computer Science and Artificial Intelligence Laboratory (CSAIL) and University of Oregon Network Startup Resource Center (NSRC).
Below are excerpts from the original proposal and a projected timeline. A general overview of the project can be found on the GMI Design Project site.
Principal Investigators: kc claffy David ClarkBradley Huffaker
Funding source: OAC-2131987 Period of performance: October 1, 2021 - September 30, 2025.
Proposal Summary
We propose to design and prototype a distributed, integrated infrastructure to measure the Internet, with the objective of improving Internet infrastructure security. The Internet’s central role in society was demonstrated vividly in 2020. While the Internet has become critical infrastructure permeating all aspects of modern society, its security and trustworthy character are subject to constant threats and attacks. The security of the Internet is a high priority for the security research community, but that community is greatly hindered by a lack of relevant data. Researchers, governments and advocates for society need a more rigorous understanding of the Internet ecosystem, a need made more urgent by the rising influence of adversarial actors. We cannot secure what we do not understand, and we cannot understand what we do not measure. As we both design the future Internet for future generations and operate the current Internet, data is lacking. Through the lens of defense systems analysis, observation (and the infrastructure to support those observations) is the basis of all defense systems. We therefore identify Internet measurement, data curation and making data usable by the research community as critical research infrastructure.
We recognize the need for an infrastructure project to support measurement of the global Internet, similar to how governments support large-scale measurements of the oceans, atmosphere, and various critical infrastructure. But the Internet sits in contrast to other critical systems, such as health care, transportation, agriculture, and commerce, where the government plays a role that complements the role of the private sector – it monitors the state of those systems, and acts as necessary to ensure that they are meeting the needs of society. The first step in this process is gathering data to understand how the system is actually working. Unfortunately, far more than other domains, the scientific enterprise of Internet security is mired in interdisciplinary challenges: complexity and scale of the infrastructure; information-hiding properties of the routing system; security and commercial sensitivities; costs of storing and processing the data; and lack of incentives to gather or share data in the first place, including cost-effective ways to use it operationally. As a result, today, operators, policy makers and citizens have no consensus view of the Internet to drive decision-making, understand the implications of current or new policies, assess the resilience of the Internet infrastructure in times of crisis, or know if the Internet is being operated in the best interests of society. Governments could gather data directly, but the trans-national character of the Internet raises challenges for government coordination. An accepted approach to data gathering and analysis is to make sure that data is made available to neutral third-parties such as academic researchers, who can independently pursue their efforts, draw their own conclusions, subject these to comparison and peer review, and present their results as advice to governments. Although we come to this challenge with open eyes, we recognize the scope of the aspiration, and thus propose a substantial 3-year MSR1 Design Project to design a Global Measurement Infrastructure to Improve Internet Security (hereafter, GMI3S-Design).
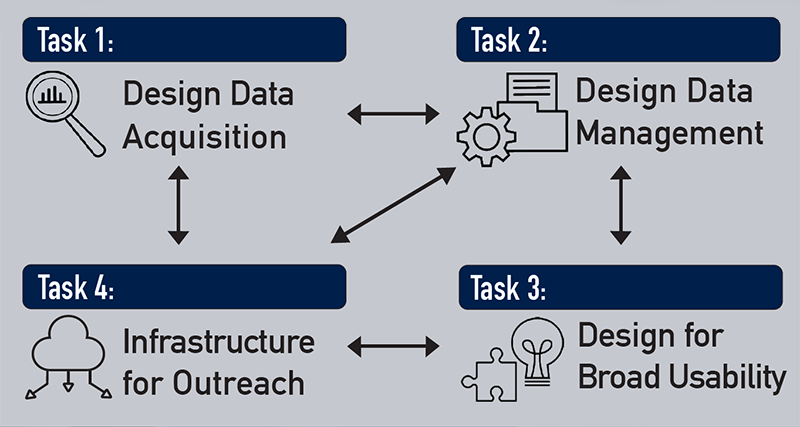
We organize our proposed work into four tasks. Our first task is to design, prototype, test and evaluate a new highly distributed network measurement platform capable of capturing several types of data relevant to security research, as well as hosting new vetted experiments. This task will require consideration of both dedicated hardware and virtualized software deployments, in a modular architecture that allows hosting sites to opt in to measurements as policy allows. Our second task includes many facets of data management: meta-data ontologies; standardizing data exchange formats; tools to support data curation and documentation; and techniques for efficient data sharing, discovery, use, and dissemination.
Our third task focuses on community-oriented infrastructure that will enable use of the data for a broad set of cybersecurity research and beyond. This task will tackle issues with sensitive data that raises privacy or corporate concerns. One subtask is to bridge the current gap between the emerging data disclosure control technologies and measurement and security practitioners. We will explore the relevance of computer science advances such as differential privacy and secure multi-party computation, to current and emerging cybersecurity research priorities. We will design a set of legal enablers, e.g., normalization of data-sharing agreements, and socialize these among our partners and the larger community as part of our fourth task, outreach. Task four will include workshops, curriculum development, and STEM/cybersecurity work force training. To prototype our design, we will work with the community of Research and Educations (R&E) networks, which interconnect campuses and research centers across the globe. The largest R&E networks in the U.S. and the EU (Internet2 and GEANT), along with ten other academic networks, have agreed to collaborate for testing and evaluation. This is a Design proposal, so many details are as yet unresolved. Reaching agreement on the specifics of the design, informed by prototype deployments, and finding and documenting working solutions is exactly the scope of this project.
Read more on the full GMI3S proposal page or as a PDF.
Projected Timeline
| Description | Projected Date | |
|---|---|---|
|
319
Task 1: Design Infrastructure for Data Acquisition |
||
| 1.1 | Report on Internet infrastructure security vulnerabilities | Mar 2022 |
| 1.2 | Complete data needs report (based on 1.1.1) | Sep 2022 |
| 1.3 | Draft monitor requirements report | Sep 2022 |
| 1.4 | Draft monitor hardware specifications report | Mar 2023 |
| 1.5 | Prototype monitor software | Sep 2023 |
| 1.6 | Initiate monitor deployment pilot | Sep 2023 |
| 1.7 | Evaluation report of Data Acquisition Component | Sep 2024 |
| 1.8 | Evaluate and prototype virtualization capabilities | Mar 2024 |
|
962
Task 2: Design Infrastructure for Data Management |
||
| 2.1 | Document data storage hardware requirement | Sep 2022 |
| 2.2 | Document data storage systems specifications | Dec 2022 |
| 2.3 | Data and metadata standards specifications (annual revisions) | Sep 2022 Sep 2023 Sep 2024 |
| 2.4 | Report on tools for data curation and documentation | Mar 2024 |
| 2.5 | Report on Data and metadata APIs | Sep 2024 |
| 2.6 | Evaluate SDK Libraries | Sep 2024 |
| 2.7 | Prototype and document data discovery tools | Sep 2023 |
| 2.8 | Document approaches to dissemination design | Sep 2023 |
|
233
Task 3: Design Community Infrastructure for Broad Usability |
||
| 3.1 | Prototype and document tools for integrating additional data sources | Sep 2024 |
| 3.2 | Document Software disclosure control approaches | Sep 2024 |
| 3.3 | Evaluate and document policy tools for disclosure control | Sep 2024 |
| 3.4 | Document extensibility case studies | Sep 2024 |
|
441
Task 4: Infrastructure for Outreach |
||
| 4.1 | Host bi-annual workshops | Feb 2022 Aug 2022 Feb 2023 Aug 2023 Feb 2024 Aug 2024 |
| 4.2 | Launch virtual collaboration environment | Oct 2021 |
| 4.2 | Evaluate and report on virtual collaboration environment | Sep 2024 |
| 4.3 | Create online course on Network Infrastructure | Sep 2023 |
| 4.4 | Create, test, evaluate, and report on course materials | Sep 2024 |
Milestones
| # | Description | Date |
|---|---|---|
| 1 | Complete Design for Data Acquisition Infrastructure | Oct 1, 2022 |
| 2 | Complete Design for Data Management Infrastructure | Oct 1, 2023 |
| 3 | Complete Design for Infrastructure for Broad Usability | Oct 1, 2024 |
| 4 | Complete Outreach and STEM Development Support Activities | Oct 1, 2024 |
| 5 | Complete infrastructure evaluation | Jun 30, 2024 |
| 6 | GMI3S-Design project completion report | Sep 30, 2024 |
Collaborators and SAC
See the GMI Design Project page for Collaborators and Strategic Advisory Council
Acknowledgment of awarding agency’s support

This material is based on research sponsored by the National Science Foundation (NSF) grant OAC-2131987. The views and conclusions contained herein are those of the authors and should not be interpreted as necessarily representing the official policies or endorsements, either expressed or implied, of NSF.
Additional Content
Designing a Global Measurement Infrastructure to Improve Internet Security (GMI3S) Proposal
Proposal for Designing a Global Measurement Infrastructure to Improve Internet Security.