Spoofer: CAIDA's Source Address Validation Measurement Project
Seeking to minimize Internet's susceptibility to spoofed DDoS attacks, we are developing and supporting open-source software tools to assess and report on the deployment of source address validation (SAV) best anti-spoofing practices. This project includes applied research, software development, new data analytics, systems integration, operations and maintenance, and an interactive analysis and reporting service.
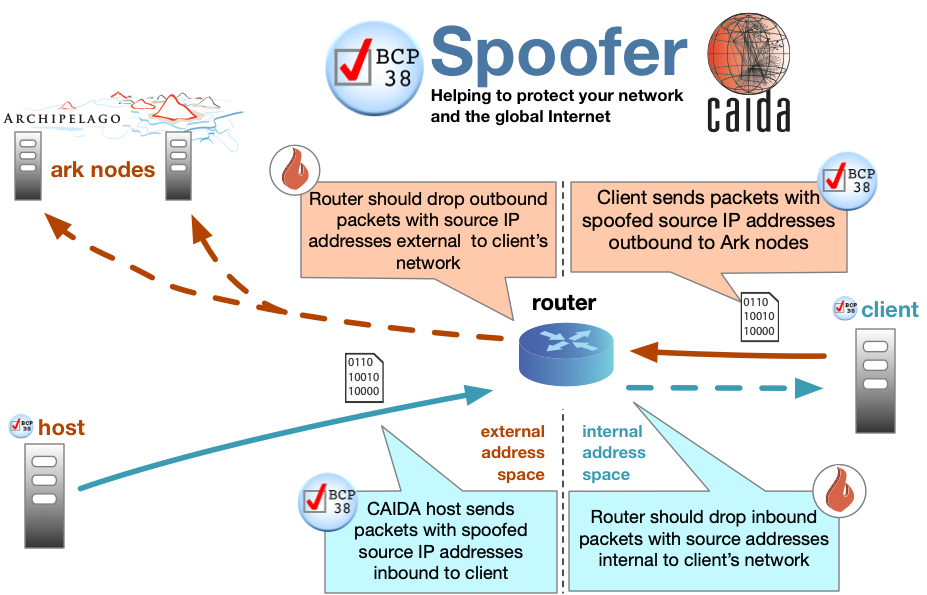
We have developed and support a new client-server system for Windows, MacOS, and UNIX-like systems that periodically tests a network's ability to both send and receive packets with forged source IP addresses (spoofed packets). We are (in the process of) producing reports and visualizations that will inform operators, response teams, and policy analysts. The system measures different types of forged addresses, including private and neighboring addresses. The test results will allow us to analyze characteristics of networks deploying source address validation (e.g., network location, business type).
Please download our Spoofer Project Brochure to learn how you can help protect your network, your customers and the Internet.
Recent updates:
Spoofer Measurement Results: Internet IP Spoofing & Filtering Summary
We generate a summary report on the current “state” of Internet IP source address spoofing/filtering using data from an active measurement tool. Thus far, we’ve collected data from thousands of clients, networks and providers. More details and published results from our research are also available.
Download Client Software
Please help! By downloading and running our client software, you’ll help advance the collective understanding of how to better protect the Internet. See screenshots of the tester in action, and a FAQ if you have questions. The following client packages are available. The sources should compile on any POSIX system. Please contact the mailing list with any issues or questions.
| Client Software Build | Description | Notes |
|---|---|---|
| Spoofer-1.4.12-win32.exe | Windows Binary Installer (signed) | |
| Spoofer-1.4.12-macos.pkg | macOS Binary Installer (signed) | |
| Spoofer-1.4.13 PPA | Ubuntu packages (signed) | apt-add-repository ppa:spoofer-dev/spoofer |
| spoofer-1.4.13.tar.gz | Source Code | |
| changelog.txt | ChangeLog |
Why does IP spoofing matter? Risks of Spoofed Source Address Attacks
Our FAQ covers common questions about spoofing relevance. The IP spoofing vulnerability is the most fundamental vulnerability of the TCP/IP architecture, which has proven remarkably scalable, in part due to the design choice to leave responsibility for security to the end hosts. Thus, the TCP/IP Internet architecture includes no explicit notion of authenticity. New spoofing-based attacks regularly appear (most recently against the DNS infrastructure) despite decades of previous exploits and prevention/tracing attempts. Current spoofing prevention mechanisms suffer from incentive issues (employing filtering does not prevent a provider from receiving spoofed source packets), deployment difficulty and management complexity. Our research seeks to inform architectural design, and security and policy mechanisms for preventing future attacks.
Watch the Video: “What is IP Spoofing?” on YouTube.
Methodology: How the Spoofer Tool Tests for IP Spoofing
The spoofer program attempts to send a series of spoofed UDP packets to servers distributed throughout the world. These packets are designed to test:
- Different classes of spoofed IPv4 and IPv6 addresses, including private and routable
- Ability to spoof neighboring, adjacent addresses
- Ability to spoof inbound (towards the client) and outbound (from the client)
- Where along the path filtering is observed
- Presence of a NAT device along the path
Request notifications of spoofing
If you would like to be notified when we detect spoofed packets from your autonomous system, please sign up on our registration page.
Spoofer in the News
- “New Internet Research Shows 30,000 Spoofing Attacks Per Day” (December 12, 2018)
- “CAIDA Spoofer Project Improves Routing Security by Publicizing Spoofed Source Address Packets” (MANRS - May 9, 2018)
- “What Role Should ISPs Play in Cybersecurity?” (Dark Reading - Apr 26, 2017)
- “DDoS defenses emerging from Homeland Security” (TechRepublic - Oct 31, 2016)
- “Hackers could use your smart home devices to launch web attacks” (Yahoo! Finance - Oct 20, 2016)
- “The Democratization of Censorship” (Krebs on Security - Sep 16, 2016)
Publications: Papers, Presentations, and Datasets
Papers
- Network Hygiene, Incentives, and Regulation: Deployment of Source Address Validation in the Internet,
Matthew Luckie, Robert Beverly, Ryan Koga, Ken Keys, Joshua Kroll, k claffy, CCS 2019. - Using Crowdsourcing Marketplaces for Network Measurements: The Case of Spoofer,
Qasim Lone, Matthew Luckie, Maciej Korczyński, Hadi Asghari, Mobin Javed, Michel van Eeten, TMA 2018. - Using Loops Observed in Traceroute to Infer the Ability to Spoof,
Qasim Lone, Matthew Luckie, Maciej Korczyński, Michel van Eeten, PAM 2017. - Previous Related Work:
- Initial Longitudinal Analysis of IP Source Spoofing Capability on the Internet,
Robert Beverly, Ryan Koga, and k claffy, Internet Society Article 2013. - Understanding the Efficacy of Deployed Internet Source Address Validation Filtering ,
Robert Beverly, Arthur Berger, Young Hyun, and k claffy, ACM SIGCOMM/USENIX IMC 2009. - Tracefilter: A Tool for Locating Network Source Address Validation Filters,
Robert Beverly and Steven Bauer, USENIX Security 2007 (poster). - The Spoofer Project: Inferring the Extent of Source Address Filtering on the Internet,
Robert Beverly and Steven Bauer, USENIX SRUTI 2005.
- Initial Longitudinal Analysis of IP Source Spoofing Capability on the Internet,
Presentations
- ACM Computer and Communications Security (CCS), Matthew Luckie, 2019.
- DHS DDoSD PI meeting, kc claffy, 2018.
- DHS R&D showcase, kc claffy, 2017.
- One Conference, kc claffy, 2017.
- DHS DDoSD PI meeting, kc claffy, 2017.
- NZNOG, Matthew Luckie, 2017.
- NANOG, kc claffy, 2016.
- SSAC, kc claffy, 2016.
- AusNOG, Matthew Luckie, 2016.
- DHS DDoSD PI meeting, Matthew Luckie, 2016.
- DHS R&D showcase, kc claffy, 2016.
- DHS S&T DDoS Defense meeting, kc claffy, 2015.
- Previous Related Work:
- IMC 2009, Robert Beverly, 2009.
- CAIDA AIMS Workshop, Robert Beverly, 2009.
- NANOG 34, Robert Beverly, 2005.
Datasets and Statistics
- Summary statistics
- Log of recent tests
- Test results classified by autonomous system
- Test results classified by country
- CAIDA IP Spoofer report highlighted by ShadowServer
Development Team
- Matthew Luckie (CAIDA): Co-PI, research, software development
- Ken Keys (CAIDA): software development
- Ryan Koga (CAIDA): Web site, analysis, testing
- Young Hyun (CAIDA): Ark infrastructure support
- k claffy (CAIDA): PI, Research, Ark support
Contact and Mailing Lists
We welcome questions and feedback to the Spoofer Information Mailing List and invite users to join the Spoofer Users Mailing List for discussion and announcements.
Funding support


The Spoofer project was sponsored by the Department of Homeland Security (DHS) Science and Technology Directorate, Homeland Security Advanced Research Projects Agency, Cyber Security Division (DHS S&T/HSARPA/CSD) BAA HSHQDC-14-R-B0005, the Government of United Kingdom of Great Britain and Northern Ireland via contract number D15PC00188. DHS funding of the Spoofer project ended in 2020, after which the project was sustained by National Science Foundation (NSF) OAC-1724853. The views and conclusions contained herein do not necessarily representing the official policies or endorsements, either expressed or implied, of DHS, NSF, the U.S. Government, or the Government of United Kingdom of Great Britain and Northern Ireland. Project originally invented and hosted by MIT ANA.
External data and tools used
Related Objects
See https://catalog.caida.org/search?query=types=software%20links=tag:caida%20spoofer to explore related objects to this document in the CAIDA Resource Catalog.
Additional Content
Spoofer Data API
This page documents the Spoofer Data API.
Spoofer: Tracefilter
Conventional wisdom dictates that ingress filtering is performed near the edges of the network rather than the core. In addition to the nature and extent of IP spoofing, we also seek to understand where in the network filtering is employed with a new, novel technique we call tracefilter.
Sample Session Traces
Sample Spoofer session traces
Sample Spoofer Screenshots
What can you expect when you run the Spoofer tester? Here, we provide screen shots.
Sample Session Report
Sample Spoofer session report
Spoofer: FAQ
Frequently Asked Questions answered about the Spoofer project.
Spoofer: History
Historical updates regarding the status of Spoofer leading up to CAIDA’s stewardship of the project.