AVOID: Automatic Verification of Internet Data-paths

Our automated system helps Department of Defense (DOD) operators who want to communicate with 5G devices by avoiding nation-state adversaries and moving communications to safe paths.
Project Summary
DOD use of commercial 5G networks entails unprecedented reliance on untrusted third-party communications infrastructure, including the 5G base stations that connect directly to 5G devices and the Internet infrastructure that underlies 5G communications. The core problem when operating through non-cooperative commercial 5G infrastructure is that the unknown infrastructure potentially exposes communications to an adversary. Traversing adversary-controlled infrastructure allows DOD’s adversaries to recognize, disrupt, or extract intelligence even from encrypted communications. Increasingly complex obfuscation techniques have created an arms race against network intelligence techniques to detect the obfuscation. With each new obfuscation, DOD can never know if it fools the adversary, or if the adversary is simply lulling DOD into a false sense of security.
We predict the next great capability leap for operating through 5G networks will be sophisticated analytics that provide situational awareness of threats within the communications infrastructure, and an implementation that dynamically routes communications along benign paths. We are not only predicting this future – we are inventing it. Our original team brought nearly a century of combined research experience in revealing and identifying unknown network infrastructure. In Phase 1, we expanded our team across disciplines and sectors to accelerate convergence on a new DOD 5G defense: restructuring communication paths to avoid adversary-controlled base stations, networks, and locations, keeping DOD communications unobservable by the adversary.
Tasks
We propose the AVOID system – Automated Verification Of Internet Data-paths (AVOID) – that creates this unprecedented capability through two deliverables that tackle two high risk attack vectors for 5G communications.
Deliverable 1 targets the potential for adversaries to control commercial base stations anywhere in the world, allowing them to subvert DOD communications at the point of entry intro the wireless network. AVOID will recognize malicious and surveillance base stations, and provide a mechanism for DOD devices to connect to specific benign base stations.
Deliverable 2 combats the ability of our adversaries to apply sophisticated and complex network analytics to any DOD communications that traverse networks or territory they control. AVOID will embed topologic and geographic awareness into a routing system, and provide a mechanism for DOD’s communications to avoid adversary-controlled territory across the global Internet and provide safe paths to DOD-controlled networks. Combined, these deliverables will provide end-to-end adversary avoidance without requiring modification to existing applications or routers in DOD networks, or cooperation by any third-party network.
Members and Partners
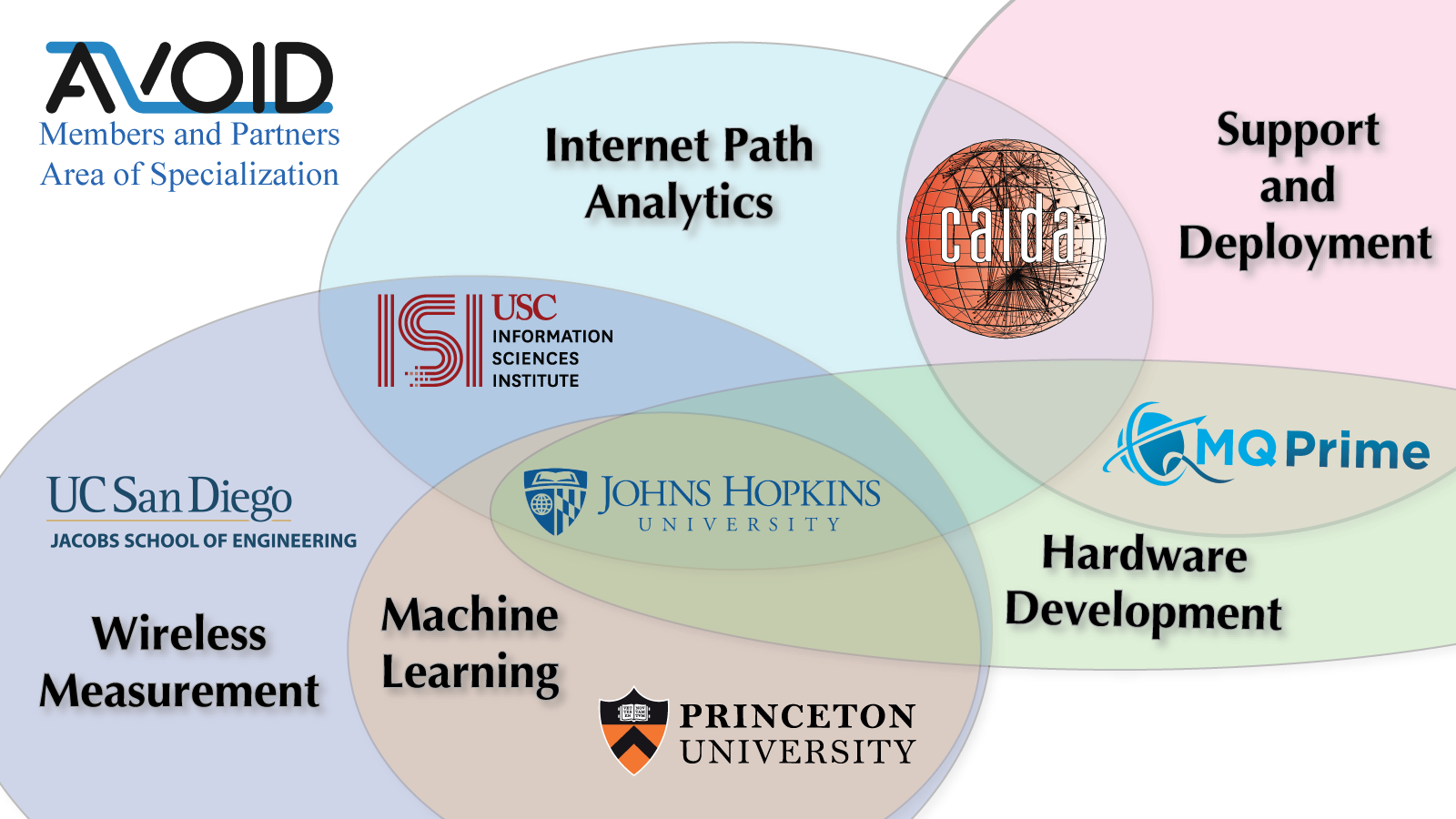
The AVOID project is led by PI Alex Marder at Johns Hopkins University, and involves a number of member institutions:
These institutions bring various areas of specialization to the AVOID project: Internet Path Analytics, Wireless Measurement, Machine Learning, Support and Development.
Funding support

Support for the Automated Verification Of Internet Data-paths for 5G project is provided by the National Science Foundation (NSF) grants ITE-2226460 5G Traffic Sovereignty: Operating Through an Adversarial Internet and ITE-2326928 Automated Verification Of Internet Data-paths for 5G. The views and conclusions contained herein are those of the authors and should not be interpreted as necessarily representing the official policies or endorsements, either expressed or implied, of NSF.







