| Project Name | Years Active |
|---|---|
|
ESCALATEEngaging Scholars in Cybersecurity Analysis: A Laboratory for Teaching and Education
The ESCALATE project will develop a centralized cybersecurity community hub that provides cyberinfrastructure-ready, data-driven cybersecurity training resources using real-world datasets.
|
2028062025 - 2028 |
|
ROOTBEERRouting Operations Observational Technology: Building to Enable Education and Research
The ROOTBEER project will build a routing observatory and operational dashboard to detect route leaks and improve the security and resilience of U.S. research and education network infrastructure.
|
2028092025 - 2028 |
|
STARNOVAScalable Technology to Accelerate Research Network Operations Vulnerability Alerts
The STARNOVA project is a translational research effort that aims to enhance the capabilities of existing NSF-funded Internet measurement infrastructure—UCSD Network Telescope (UCSD-NT)—to strengthen the security of CI hosted at the San Diego Supercomputer Center (SDSC).
|
2026072023 - 2026 |
|
AVOIDAutomated Verification Of Internet Data-paths for 5G
Automatic Verification of Internet Data-paths (AVOID) will automatically shift communications from unsafe paths potentially under adversary control to verified safe paths.
|
ongoing |
|
RABBITSA Toolkit for Reproducible Assessment of Broadband Internet Topology and Speed
A project to develop a new measurement toolkit for assessing broadband internet topology and speed, enabling consistent and reproducible tests across platforms.
|
2026092023 - 2026 |
|
Cloud BottlenecksDetection and Analysis of Infrastructure Bottlenecks in a Cloud-Centric Internet
This project proposes an effort to design measurement and analysis tools to reveal performance bottlenecks outside the cloud networks where the high cost of deployment and operations leads to infrastructure bottlenecks for cloud applications.
|
2026092022 - 2026 |
|
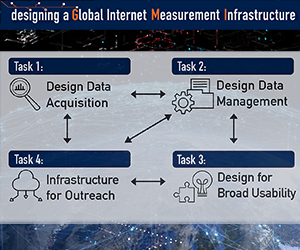
GMIDesigning a Global Measurement Infrastructure to Improve Internet Security
A design project to prototype a distributed, integrated infrastructure to measure the Internet, with the objective of improving Internet infrastructure security.
|
ongoing |
| zzz
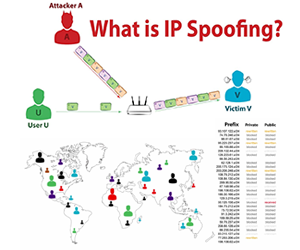
STARDUSTSustainable Tools for Analysis and Research on Darknet Unsolicited Traffic
Measuring the Internet's susceptibility to spoofed source address IP packets, we generate a summary report on the current "state" of Internet IP source address spoofing/filtering using data from an active measurement tool.
|
2021032017 - 2021 |
|
Spoofer
Measuring the Internet's susceptibility to spoofed source address IP packets, we generate a summary report on the current "state" of Internet IP source address spoofing/filtering using data from an active measurement tool.
|
ongoing |
|
Cloudtrace
The CloudTrace project investigates how cloud networks interconnect and interact with the public Internet.
|
ongoing |
|
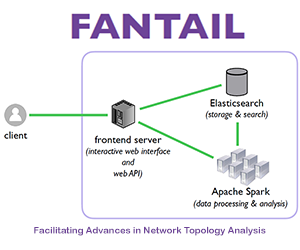
FANTAILFacilitating Advances in Network Topology Analysis
The FANTAIL system aims to enable discovery of the full potential value of massive raw Internet end-to-end path measurement data sets.
|
ongoing |
| zzz
KISMETKnowledge of Internet Structure: Measurement, Epistemology, and Technology
This page describes KISMET, a CAIDA project of the NSF Convergence Accelerator program.
|
2020052019 - 2020 |
| zzz
MANICMeasurement and ANalysis of Internet Congestion
The MANIC project -- Measurement and Analysis of Interdomain Congestion -- has developed a prototype system to monitor interdomain links and their congestion state, in order to provide empirical grounding to debates related to interdomain congestion.
|
2022032017 - 2022 |
| zzz
IODAInternet Outage Detection and Analysis
CAIDA developed an operational prototype system that monitors the Internet, in near-realtime, with the goal of identifying macroscopic Internet outages affecting the edge of the network, i.e., significantly impacting an AS or a large fraction of a country.
|
2020012012 - 2020 |
| zzz
IMPACTInformation Marketplace for Policy and Analysis of Cyber-risk & Trust
The Information Marketplace for Policy and Analysis of Cyber-risk & Trust (IMPACT) project provides vetted researchers with current network operational data.
|
2020082012 - 2020 |
| zzz
NDN-NPNamed Data Networking Next Phase
Named Data Networking is a proposed Internet architecture that replaces IP with a network layer that routes directly on content names.
|
2017042014 - 2017 |
| zzz
IRNC-SPIRNC Special Project
The goal of this IRNC Special Project was to identify and support the measurement priorities of the International Research Network Connections community.
|
2014022010 - 2014 |
|
Network Telescope
Monitoring of traffic through network telescopes, or portions of routed IP address space on which little or no legitimate traffic exists.
|
ongoing |
| zzz
IPv6 Evolution
A measurement-driven exploration of the evolution of IPv6.
|
2016042012 - 2016 |
| zzz
NDNNamed Data Networking
Named Data Networking is a proposed Internet architecture that replaces IP with a network layer that routes directly on content names.
|
2014082010 - 2014 |
| zzz
Economics of Internet Interconnection
From 2010-2013, CAIDA performed a study of the economics of Internet interconnection.
|
2013072010 - 2013 |
| zzz
CybersecurityCybersecurity
The Cybersecurity project proposes to develop and implement new measurement and data collection technologies to understand and protect essential U.S. informational infrastructure.
|
2019072012 - 2019 |
| zzz
SD-NAPSan Diego Network Access Point
The purpose of the SD-NAP is to facilitate efficient interconnection of Internet Protocol transit networks within and to the San Diego Local Access and Transport Area, California LATA 6, and to provide a platform for traffic analysis by CAIDA researchers, with the goal of promoting a robust, scalable global Internet infrastructure.
|
2000121998 - 2000 |
| zzz
DatCatInternet Measurement Data Catalog
The goal of the Trends project is to create and populate the Internet Measurement Data Catalog (IMDC) that will facilitate access, archiving, and long-term storage of Internet data as well as sharing the data among Internet researchers.
|
2018062002 - 2018 |
| zzz
ITLInternet Teaching Laboratories
As an extension of the IEC project, CAIDA helped develop Internet Teaching Laboratory (ITL) facilities at several U.S. colleges and universities.
|
2002091998 - 2002 |
| zzz
Internet Atlas
The Internet Atlas project involved developing techniques, software, and protocols for mapping the Internet, focusing on Internet topology, performance, workload, and routing data. It also includes assessment of state-of-the-art in this nascent sector.
|
2004121999 - 2004 |
| zzz
IECInternet Engineering Curriculum Repository
The Internet Engineering Curriculum Repository is a projectto help educators and others interested in Internet technology keep up with developments in the field.
|
2002091998 - 2002 |
| zzz
DNS AnalysisAnalysis of the DNS root and gTLD nameserver system
We conducted passive and active measurements of the DNS root servers behavior, connectivity and performance. We also analyzed data collected at the servers themselves.
|
2002122001 - 2002 |
|
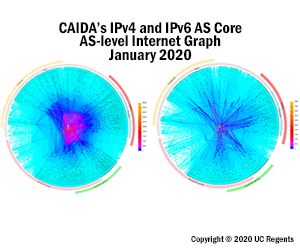
AS Core Visualization
We generate Internet Topology Maps, also referred to as AS-level Internet Graphs, in order to visualize the shifting topology of the Internet over time.
|
ongoing |
| zzz
Macroscopic Topology Measurements
CAIDA researchers have been collecting connectivity and latency data for a wide cross-section of the commodity Internet since 1998 for the IPv4 address space and since 2003 for the IPv6 address space. We use these data to derive maps of the Internet at various granularity levels: IP, router, AS.
|
2018121998 - 2018 |
|
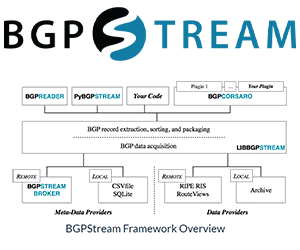
ArkArchipelago Measurement Infrastructure
Archipelago (Ark for short) is CAIDA's next-generation active measurement infrastructure and represents an evolution of the skitter infrastructure.
|
ongoing |
| zzz
DITLA Day in the Life of the Internet
DITL is a product of the effort of CAIDA, ISC, DNS-OARC, many partnering root nameserver operators and other organizations to coordinate and conduct large-scale, simultaneous traffic data collection events with the goal of capturing datasets of strategic interest to researchers.
|
2009042002 - 2009 |
| zzz
Bandwidth Estimation
We propose to improve existing techniques and tools for bandwidth estimation, and to test and integrate them into Department of Energy (DOE) and other network infrastructures. The proposed effort will overcome limitations of existing algorithms whose estimates degrade as the distance from the probing host increases.
|
2004102001 - 2004 |
Projects and Infrastructure
To press forward its mission of promoting the engineering and maintenance of a robust, scalable Internet, CAIDA focuses its resources on various projects and areas of strategic interest. These pages document the plans and status for these projects.